Introduction
In this tutorial I will discuss how SiteMinder works as an SSO authentication system. This tutorial will give you technical insights of the working principle of SiteMinder system. The Web Application Firewall may integrate with SiteMinder to provide single sign-on and centralized management of web applications using the predefined security policies. It uniquely identifies a user before the user is authenticated as named user, and manages user’s privileges to ensure that the user access only authorized applications or operations.
In SiteMinder single sign-on (SSO), a user successfully authenticates through one agent and does not need to re-authenticate when accessing a realm protected by a different agent. The two agents must be in the same cookie domain, for example: /xyz.siteminder.com.
Problem – Duplicate Logins
There may be situations where users access a web service which is, for example, hosted on a Apache Web server and users are authenticated by some authentication mechanism, let’s say, LDAP.
If the same users want to access a web service on an IIS Web server, they have to be authenticated by another mechanism, let’s say , Windows domain controller.
Since there is no way to pass authentication verification between these two systems, users must log in twice in different system to authenticate themselves.
Solution
In such situation, SiteMinder comes to play a vital role to these multiple login problems by providing a centralized access point called SSO (Single Sing-On) for all authentication mechanisms.
Instead of being authenticated by each web service in different systems, users are authenticated by SiteMinder system.
Once the user has been authenticated, a special encrypted cookie is created and used for subsequent logins to different web-based services and applications.
Even though users are automatically authenticated, you can curtail their access rights to specific resources by establishing access control policies through SiteMinder’s security policy management features.
Components of SiteMinder
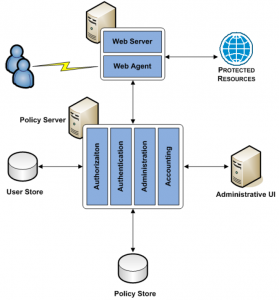
SiteMinder system mainly consists of Web Agent and Policy Server.
Web Agent:
- Web Agent, ERP Agent, Secure Proxy Agent etc.
Policy Server:
- User store, Policy store – DB/LDAP.
- Session and key store – DB/LDAP.
An Web Agent is a component that allows the web server to be managed by SiteMinder. Web Agents are generally integrated with a standard web server or application server that enables SiteMinder to manage web applications based on the predefined security policies.
Web Agent is integrated with a standard web server and just a filter that intercepts all requests for resources (URLs) to a web server, then decides whether the specified resource is under SiteMinder’s control or protected.
If the resource is protected, the Policy Server is contacted. If the resource is not protected or not under SiteMinder’s control, the request will go directly into web server.
Policy Server provides policy management and functions for authentication within the SiteMinder framework. The Policy Server provides authentication to web-based applications. Policy Server provides both authentication and authorization for a user. The Policy Server acts as a front end to whatever authentication method is being deployed within an organization.
The following points which are provided by policy server:
- Basic authentication (user-name/password)
- Basic authentication over SSL
- Authentication schemes
- ACE/Server (Security Dynamics)
- CryptoCard
- RADIUS Proxy
- Forms-based authentication
- X.509 certificates
- Custom or third-party schemes
How SiteMinder works
If those resources are not protected then Web Agent allows the web site or app to proceed and return the requested page to the user.
If resource is protected and user is not authenticated then web app returns an Access Denied error.
If resource is protected and user is not authorized then web app returns an Access Denied error.
The following steps explain how Siteminder works if the resource is protected:
- User requests a web page or a resource
- Web Agent intercepts the request
- Web Agent verifies with Policy Server if the request is protected
- Policy Server checks the policy and rules applicable for the incoming request; accordingly protection information and one of the authentication methods is returned
- Policy Server asks Web Agent for user credentials (using form based authentication, token or any other authentication method). Credentials are generally username and password
- Web Agent passes supplied authentication information to Policy Server and asks Policy Server if user is authenticated
- Policy Server checks user information on file and verified against the supplied user credentials
- Policy Server also checks policy and rules for authenticating the user
- Policy Server informs Web Agent that user is authorized and passes the response data
- If not authenticated then Web Agent asks for credentials (using form based authentication, token or any other authentication method).
- Web Agent allows web app to process user’s request and provides response data
- Once the user is authenticated successfully, an encrypted cookie or user credential is created and passed to the web server
- Web page or resource is processed and returned to user
- When the same user tries to access a URL on web server, the Web Agent can then grant access according to the user credential it was passed, eliminating the need for a second time login.
Limitations of Siteminder
- When a user logs into a computer and authentication handled by operating system, then you cannot pass user information to SiteMinder because SiteMinder was designed to work in a web server environment, where authentication is triggered upon a URL request.
- Though SiteMinder is a valuable tool for SSO (Single Sign-On) login between disparate web applications, the user is still required to log into the platform from which the web applications will be launched. SiteMinder also requires that an agent be installed on each web server that will participate in the SSO environment.
That’s all about the working principle of SiteMinder authentication system.
very well explained
Hi I need siteminder tutorial